I got tasked with installing a brand new Windows Server 2019 with the Remote Desktop Services (RDS) role. It was a pretty straightforward installation, but minor things might work differently compared to previous versions of Windows Server (I was migrating off Windows Server 2012 R2).
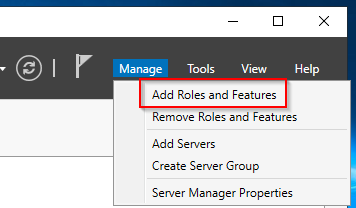
Start by adding the RDS role through Server Manager.
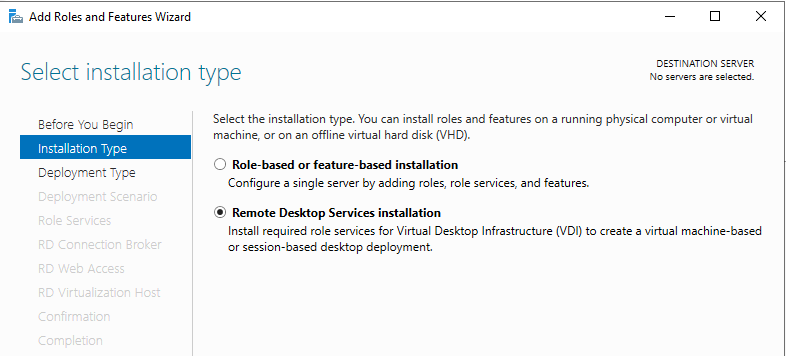
Select the RDS installation:
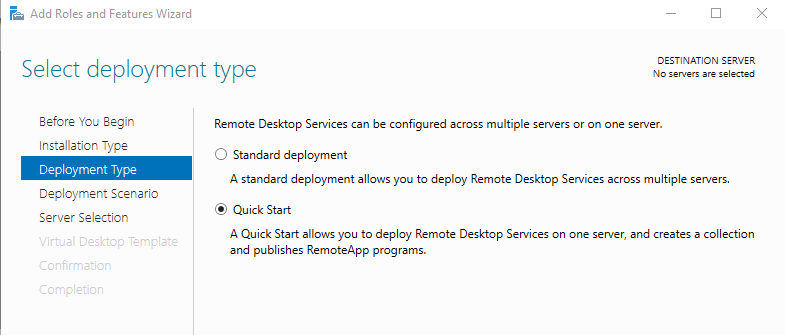
I went for the Quick Start because my deployment is fairly basic.
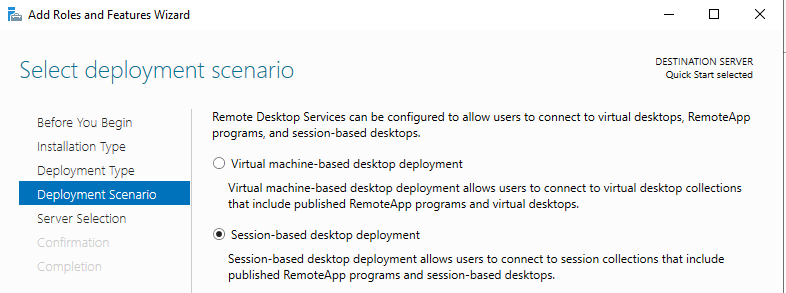
Session-based deployment enables multi-session support on the server.
The server should be automatically selected.
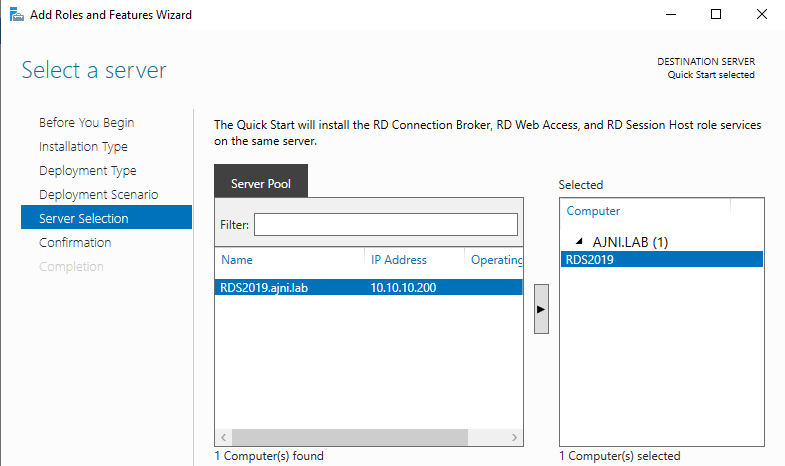
The three roles (RD Connection Broker, RD Web Access and RD Session Host) will be installed.
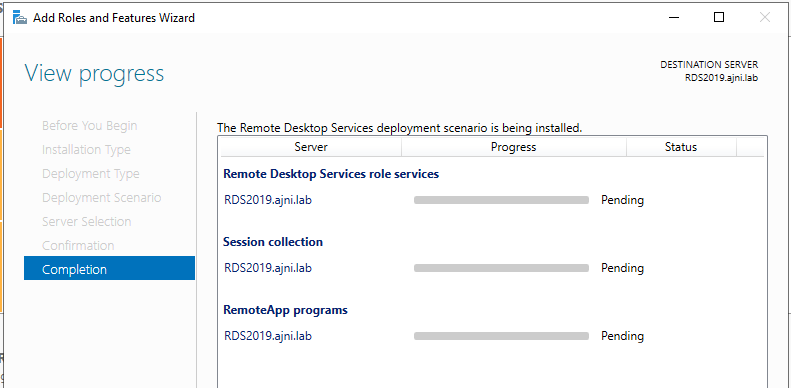
After the installation a license warning will be shown in the Notification Center.

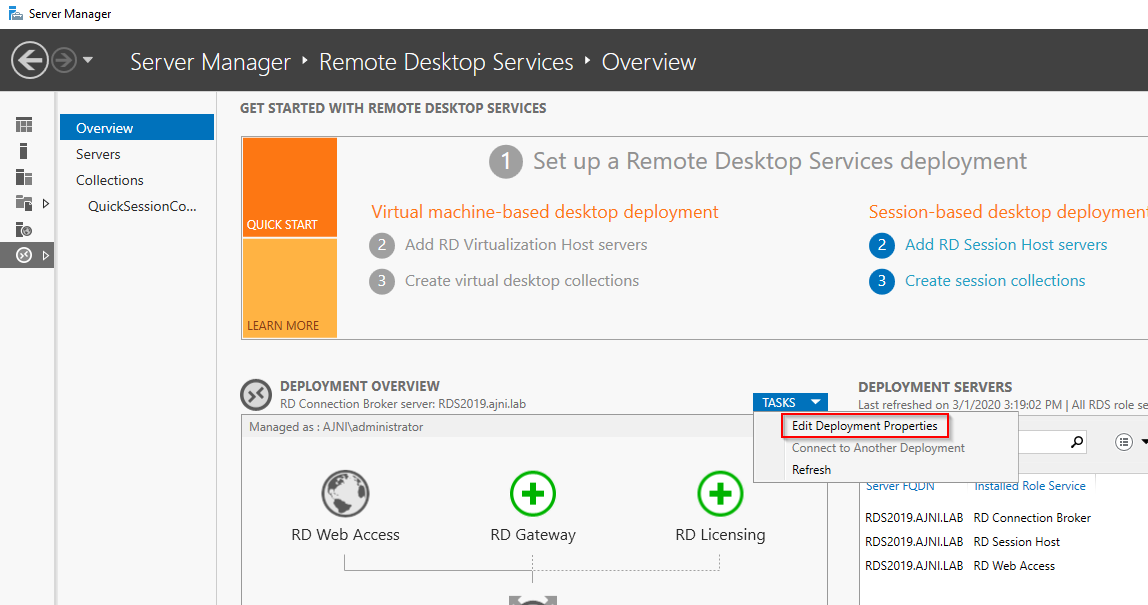
Two things are needed in order for licensing to work properly: The license server and licensing mode.
In a production environment, usually there is a separate server hosting the RDS Licensing service.
Server Manager > Remote Desktop Services > Overview > Tasks > Edit Deployment properties
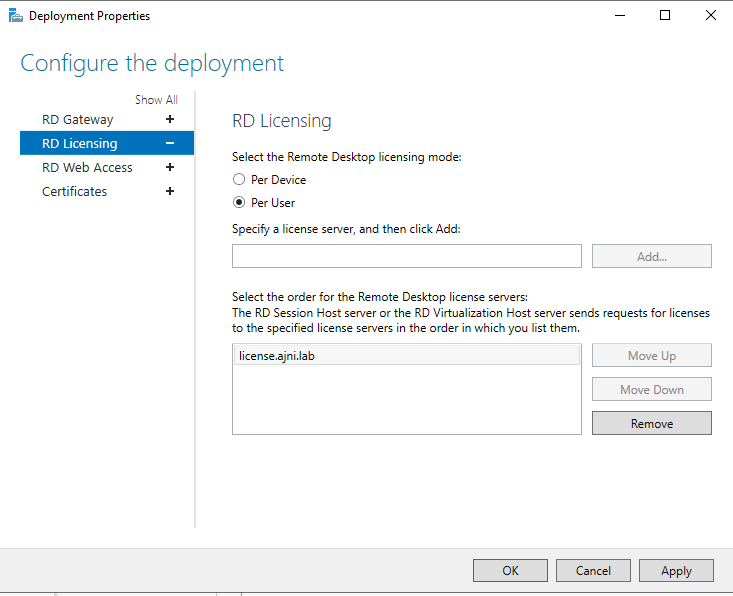
I had problems with the licensing mode not being applied properly. This registry key worked wonderfully though:
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\Terminal Server\RCM\Licensing Core
DWORD LicensingMode
4 = Per user
2 = Per Device
The license server can be also set through the registry:
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Services\TermService\Parameters\LicenseServers
REG_MULTI_SZ SpecifiedLicenseServers = license.ajni.lab
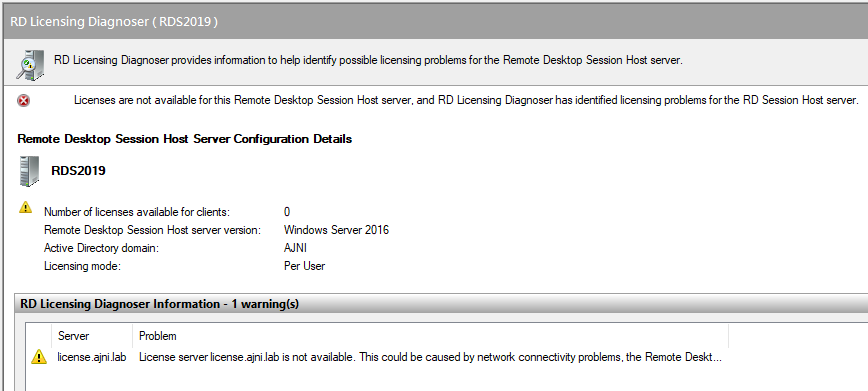
With RD Licensing Diagnoser you can check for potential errors (can be opened through Server Manager > Tools > Remote Desktop Services).
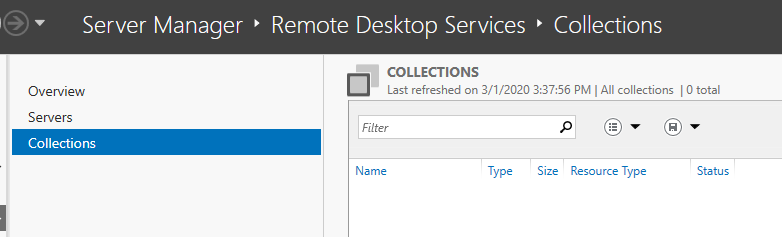
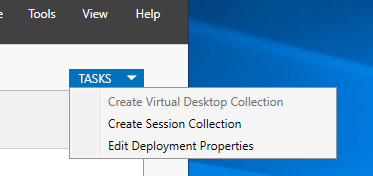
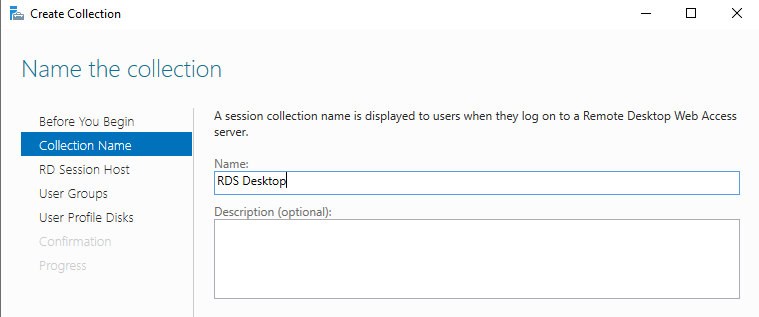
Now on to the last step: Create a custom device collection.
Server Manager > Remote Desktop Services > Collections > Tasks > Create Session Collection
This is also pretty straight forward stuff.
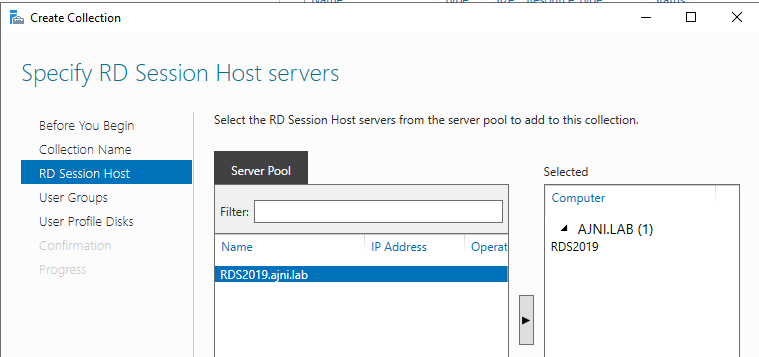
Make sure you select the server by moving it to the right with the arrow.
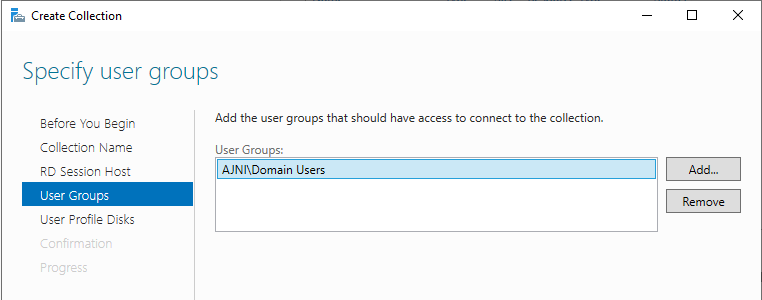
In a production environment a custom group should be used to control the number of permitted users.
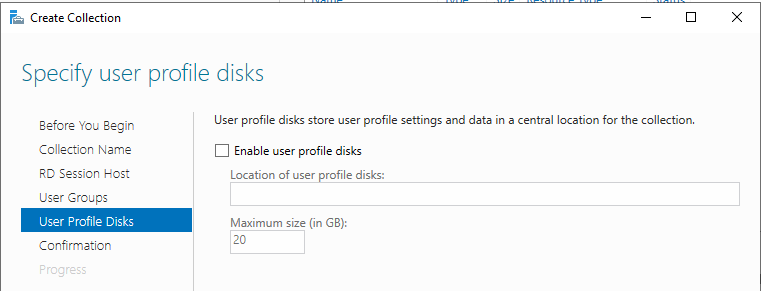
User profile disks were not needed in my environment.
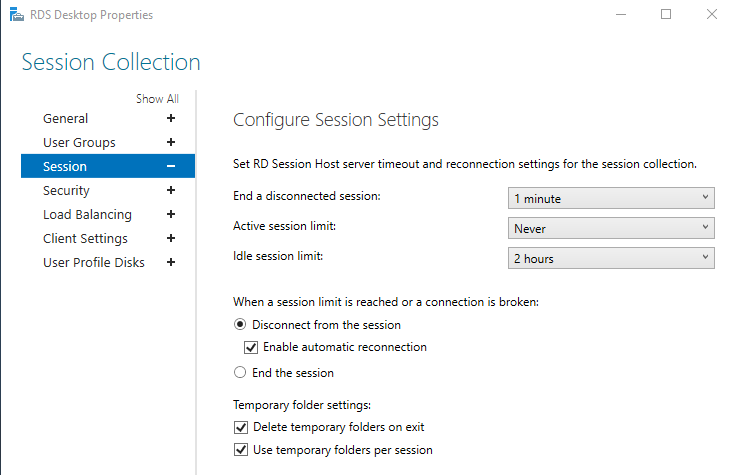
After the creation, there are some things that should be changed in the Collection properties (Server Manager > Remote Desktop Services > Collections > Collection Name):
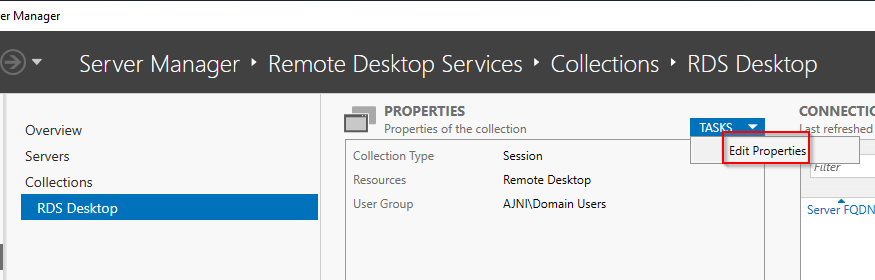
These are my specific settings, you should change the parameters based on your experience or leave them at their default values.
Older clients might have problems with these security settings (like Network Level Authentication – NLA)
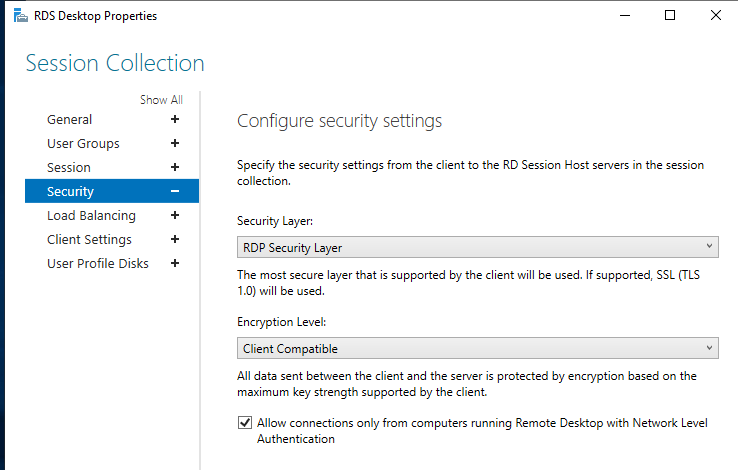
Do not forget to apply the changes.
Bonus:
If you have specific AD user attributes, like the home folder or program auto-start, they will not work because of changes made to RDS 2016/2019. You can read this article from Microsoft’s website: https://support.microsoft.com/en-us/help/3200967/changes-to-remote-connection-manager-in-windows-server
Following registry entries will tell the Remote Desktop Session Host (RDSH) to query AD DS for RDP profile settings:
HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows NT\Terminal Services
Name: fQueryUserConfigFromDC
Type: Reg_DWORD
Value: 1
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\Terminal Server\WinStations\RDP-tcp
Name: fQueryUserConfigFromDC
Type: Reg_DWORD
